Analysis
The Great Tariff Pivot: How the 2026 Trade Clash is Reshaping the Global Economic Order

For a fleeting moment on Friday morning, corporate America let out a collective sigh of relief. The highest court in the land had just dismantled the cornerstone of the administration’s sweeping trade agenda, sending equity markets into a celebratory climb. But in the modern era of executive trade policy, relief is a highly perishable commodity.
By Saturday morning, the narrative had violently fractured. The Trump tariff hike 2026 was officially underway, replacing a permanent, legally fraught tax with a temporary, legally untested one. Over a frantic 48-hour window, global markets experienced severe fiscal whiplash as the administration executed a US global tariff increase from 10% to 15%, pivoting from the ashes of one statute to the obscure remnants of another.
To understand the profound impact of Trump tariffs on global economy dynamics, one must look beyond the immediate headlines. This is not merely a story about import taxes; it is a profound constitutional tug-of-war over the power of the purse, the mechanics of global supply chains, and a 150-day ticking clock that will define the geopolitical landscape ahead of the midterm elections.
The 6-3 Bombshell: The Supreme Court Ruling Against Trump Tariffs
The catalyst for this weekend’s economic tremor was a landmark decision handed down on February 20, 2026. In a definitive 6-3 decision authored by Chief Justice John Roberts, the Supreme Court ruling against Trump tariffs struck down the administration’s reliance on the International Emergency Economic Powers Act (IEEPA) of 1977.
For over a year, IEEPA had been the sledgehammer of the “America First” trade doctrine, justifying baseline tariffs of up to 50% on nearly all US trading partners by classifying persistent trade deficits as a “national emergency.” However, the Court—relying heavily on the major questions doctrine—ruled unequivocally that Congress never intended to delegate broad taxing authority to the executive branch under an emergency sanctions law.
The economic fallout of this ruling is staggering. According to estimates cited by the Tax Foundation, the administration had illegally collected an estimated $160 billion in tariff revenue. The Supreme Court did not address the logistical nightmare of refunding these billions, leaving the US Court of International Trade to untangle what Justice Brett Kavanaugh, in his dissent, accurately warned would be a “mess.”
For a few hours, Wall Street celebrated the erasure of what amounted to the largest consumer tax increase in a generation. Shares of legacy automakers, retailers, and consumer goods conglomerates surged. But the celebration ignored a fundamental reality of Washington: executive power, once exercised, rarely retreats without a fight.
The Section 122 Pivot and the Truth Social Escalation
Faced with the largest judicial defeat of his renewed tenure, President Trump immediately sought alternative statutory armor. On Friday evening, he signed an executive order invoking Section 122 of the Trade Act of 1974 to impose a 10% global tariff.
But by Saturday morning, the administration decided that 10% was insufficient. Taking to social media, Trump calls court decision anti-American—labeling the 6-3 ruling “ridiculous” and “poorly written”—and immediately escalated the stakes. He announced a US global tariff increase from 10% to 15%, the absolute maximum allowed under Section 122.
This obscure, never-before-used provision allows the president to impose a temporary import surcharge to deal with “large and serious United States balance-of-payments deficits.” However, trade scholars at the Peterson Institute for International Economics point out a glaring vulnerability: Section 122 was drafted during the collapse of the Bretton Woods system to protect fixed exchange rates. Because the United States has operated on a floating exchange rate since 1973, many economists argue the legal predicate for a “balance-of-payments crisis” simply does not exist.
More importantly, Section 122 comes with a strict expiration date. The 15% tariff can only last for 150 days unless Congress explicitly votes to extend it. This sets up a massive fiscal cliff in late August 2026, dropping this economic grenade squarely into the lap of the midterm election cycle.
The Impact of Trump Tariffs on Global Economy and Markets
The immediate impact of Trump tariffs on global economy metrics has been a cocktail of volatility and defensive posturing. The Trump tariff hike 2026 fundamentally shifts the burden from a permanent structural tax to a short-term, high-intensity shock.
- Market Volatility: While traditional equities initially rallied on the Supreme Court news, the Saturday escalation triggered a defensive retreat in futures markets. Notably, Bitcoin and other crypto assets slipped over the weekend as investors rotated into traditional safe havens like gold and short-term Treasuries, spooked by the unpredictability of the executive branch’s trade mechanisms, as tracked by The Wall Street Journal.
- Supply Chain Paralysis: A 150-day tariff of 15% acts as a freeze on global logistics. Importers cannot easily alter supply chains in a five-month window. Instead, businesses are forced to absorb the cost, halt overseas orders, or pass the 15% surcharge directly to consumers, risking a localized inflation spike just as the Federal Reserve has struggled to maintain its 2% target.
- Geopolitical Friction: International trading partners, who cautiously welcomed Friday’s court ruling, are now bracing for the August cliff. As analysts at Chatham House note, the European Union, the UK, and Asian manufacturing hubs are preparing retaliatory measures should the US attempt to migrate these temporary Section 122 tariffs into permanent Section 301 tariffs (which require a lengthy investigation into “unfair” trade practices).
Visualizing the Trade War: Tariff Authority Breakdown
To understand the legal gymnastics of the past 48 hours, one must look at the varying statutes the executive branch has weaponized to bypass Congressional taxation.
| Tariff Authority | Status as of Feb 21, 2026 | Max Rate Applied | Duration / Limits | Key Distinctions |
| IEEPA (1977) | Struck Down by Supreme Court | Up to 50% | Indefinite | Required a declared “national emergency.” The Court ruled it unconstitutional for tariff implementation. |
| Section 122 (1974) | Active via Executive Order | 15% | 150 Days | Intended for balance-of-payments deficits. Extension requires an act of Congress. |
| Section 232 (1962) | Active | Variable (25% Steel) | Indefinite | Justified under “national security.” Unaffected by the recent Supreme Court ruling. |
| Section 301 (1974) | Under Investigation | Variable | Indefinite | Targets “unfair” trade practices. Requires formal review by the USTR. Likely the administration’s next pivot. |
Export to Sheets
Economic Projections: The 150-Day Cliff
What happens when the 150-day clock strikes zero in late August 2026? This is the multi-trillion-dollar question dominating trading desks from Wall Street to the City of London.
The strategy is clear: the administration is using the temporary 15% Section 122 tariff as a fiscal bridge. During these five months, the US Trade Representative (USTR) will likely fast-track investigations under Section 301, a far more legally insulated statute that permits permanent tariffs against countries engaged in “unjustifiable” trade practices.
However, cramming a comprehensive Section 301 investigation into 150 days is administratively Herculean. If the administration fails to formalize new, legally sound tariffs before Section 122 expires, they will face a hostile Congress entirely unwilling to vote for a tariff extension just weeks before the November midterms. According to researchers at the Brookings Institution, passing a tariff extension through a divided legislature under these circumstances has a statistical probability nearing zero.
This leaves the global economy in a state of suspended animation. Corporations are effectively paying a 15% premium to access the American consumer market, with no guarantee of whether that toll will vanish in August or become a permanent fixture of a deglobalized world.
Conclusion: The New Reality of Weaponized Trade
The events of February 20-21, 2026, will be studied in economic textbooks for decades. We witnessed the judicial system successfully rein in executive overreach, only to watch the executive branch instantly exploit a 50-year-old legislative loophole to achieve the exact same economic end.
The Supreme Court ruling against Trump tariffs was a victory for constitutional purists, but it offered little practical solace to the global supply chain. The resulting US global tariff increase from 10% to 15% ensures that the era of weaponized trade policy is far from over—it has merely changed its legal letterhead. As the 150-day countdown begins, businesses and consumers alike are left bracing for the impact of a profoundly uncertain summer.
Discover more from The Economy
Subscribe to get the latest posts sent to your email.
Analysis
Is Anthropic Protecting the Internet — or Its Own Empire?

Anthropic Mythos, the most powerful AI model any lab has ever disclosed, arrived this week draped in the language of altruism. Project Glasswing — the initiative through which a curated circle of Silicon Valley aristocrats gains exclusive access to Mythos — is pitched as an act of civilizational defense. The framing is elegant, the mission is genuinely urgent, and at least part of it is true. But behind the Mythos AI release lies a second story that Dario Amodei’s beautifully worded blog posts conspicuously omit: Mythos is enterprise-only not merely because Anthropic fears hackers, but because releasing it to the open internet would trigger the single greatest act of industrial-scale capability theft in the history of technology. The cybersecurity rationale is real. The economic motive is realer still. Understanding both is how you understand the AI industry in 2026.
What Anthropic Mythos Actually Does — and Why It Terrified Silicon Valley
To appreciate the gatekeeping, you must first reckon with the capability. Mythos is not an incremental model. It occupies an entirely new tier in Anthropic’s architecture — internally designated Copybara — sitting above the public Haiku, Sonnet, and Opus hierarchy that most developers work with. SecurityWeek’s detailed technical breakdown describes it as a step change so pronounced that calling it an “upgrade” is like calling the internet an “improvement” on the fax machine.
The numbers are staggering. Anthropic’s own Frontier Red Team blog reports that Mythos autonomously reproduced known vulnerabilities and generated working proof-of-concept exploits on its very first attempt in 83.1% of cases. Its predecessor, Opus 4.6, managed that feat almost never — near-0% success rates on autonomous exploit development. Engineers with zero formal security training now tell colleagues of waking up to complete, working exploits they’d asked the model to develop overnight, entirely without intervention. One test revealed a 27-year-old bug lurking inside OpenBSD — an operating system historically celebrated for its security — that would allow any attacker to remotely crash any machine running it. Axios reported that Mythos found bugs in every major operating system and every major web browser, and that its Linux kernel analysis produced a chain of vulnerabilities that, strung together autonomously, would hand an attacker complete root control of any Linux system.
Compare that to Opus 4.6, which found roughly 500 zero-days in open-source software — itself a remarkable achievement. Mythos found thousands in a matter of weeks. It then attempted to exploit Firefox’s JavaScript engine and succeeded 181 times, compared to twice for Opus 4.6.
This is also, importantly, what a Claude Mythos vs open source cybersecurity comparison looks like at full resolution: no freely available model comes remotely close, and Anthropic knows it. That gap is the entire product.
The Official Narrative: “We’re Protecting the Internet”
The Anthropic enterprise-only AI decision is framed through Project Glasswing as a coordinated defensive effort — an attempt to patch the world’s most critical software before capability equivalents proliferate to hostile actors. Anthropic’s official Glasswing page commits $100 million in usage credits and $4 million in direct donations to open-source security organizations, with founding partners that read like a geopolitical alliance: Amazon, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, and Palo Alto Networks. Roughly 40 additional organizations maintaining critical software infrastructure also gain access. The initiative’s name — Glasswing, after a butterfly whose transparency makes it nearly invisible — is a metaphor for software vulnerabilities that hide in plain sight.
The security rationale for why Anthropic limited Mythos is not confected. In September 2025, a Chinese state-sponsored threat actor used earlier Claude models in what SecurityWeek documented as the first confirmed AI-orchestrated cyber espionage campaign — not merely using AI as an advisor but deploying it agentically to execute attacks against roughly 30 organizations. If that was possible with Claude’s then-current models, what becomes possible with a model that autonomously chains Linux kernel exploits at a near-perfect success rate?
Anthropic’s Logan Graham, head of the Frontier Red Team, captured the threat succinctly: imagine this level of capability in the hands of Iran in a hot war, or Russia as it attempts to degrade Ukrainian infrastructure. That is not science fiction. It is the calculus driving the controlled release. Briefings to CISA, the Commerce Department, and the Center for AI Standards and Innovation are real, however conspicuously absent the Pentagon remains from those conversations — a pointed omission given Anthropic’s ongoing legal war with the Defense Department over its blacklisting.
So yes: the security case is genuine. But it is, at most, half the story.
The Distillation Flywheel: Why Frontier Labs Are Really Gating Their Best Models
Here is the economic argument that no TechCrunch brief or Bloomberg data point has assembled cleanly: Anthropic model distillation is an existential threat to the frontier lab business model, and Mythos is as much a response to that threat as it is a cybersecurity initiative.
The mathematics of adversarial distillation are brutally asymmetric. Training a frontier model costs approximately $1 billion in compute. Successfully distilling it into a competitive student model costs an adversary somewhere between $100,000 and $200,000 — a 5,000-to-one cost advantage in the favor of the copier. No rate-limiting policy, no terms-of-service clause, and no click-through agreement closes that gap. The only defense is controlling access to the teacher in the first place.
Frontier lab distillation blocking is not a new concern, but 2026 has given it terrifying specificity. Anthropic publicly disclosed in February that three Chinese AI laboratories — DeepSeek, Moonshot AI, and MiniMax — collectively generated over 16 million exchanges with Claude through approximately 24,000 fraudulent accounts. MiniMax alone accounted for 13 million of those exchanges; Moonshot AI added 3.4 million; DeepSeek, notably, needed only 150,000 because it was targeting something far more specific: how Claude refuses things — alignment behavior, policy-sensitive responses, the invisible architecture of safety. A stripped copy of a frontier model without its alignment training, deployed at nation-state scale for disinformation or surveillance, is the nightmare scenario that animated Anthropic’s founding. It may now be unfolding in real time.
What does this have to do with Mythos being enterprise-only? Everything. A model that autonomously writes working exploits for every major OS would, if released via standard API access, provide Chinese distillation campaigns with not just conversational capability but offensive cyber capability — the very thing that makes Mythos commercially unique. Releasing Mythos at scale would be, simultaneously, the greatest act of market self-destruction and the greatest gift to adversarial state actors in the history of enterprise software. Enterprise-only access eliminates both risks at once: it monetizes the capability at maximum margin while denying it to the distillation ecosystem.
This is the distillation flywheel in action. Frontier labs gate the highest-capability models behind enterprise contracts; enterprises pay premium rates for exclusive capability access; the revenue funds the next generation of training runs; the new model is again too powerful to release openly. Each rotation of the wheel deepens the competitive moat, raises the enterprise price floor, and tightens the grip of the three dominant labs over the global AI stack.
Geopolitics at the Model Layer: The Three-Lab Alliance and the New AI Cold War
The Mythos security exploits announcement arrived within 24 hours of a Bloomberg-reported development that is arguably more consequential for the global technology order: OpenAI, Anthropic, and Google — three companies that have spent the better part of three years competing to annihilate each other — began sharing adversarial distillation intelligence through the Frontier Model Forum. The cooperation, modeled on how cybersecurity firms exchange threat data, represents the first substantive operational use of the Forum since its 2023 founding.
The breakdown of what each Chinese lab extracted from Claude reveals something remarkable: three entirely different product strategies, fingerprinted through their query patterns. MiniMax vacuumed broadly — generalist capability extraction at scale. Moonshot AI targeted the exact agentic reasoning and computer-use stack that its Kimi product has been marketing since late 2025. DeepSeek, with a comparatively tiny 150,000-exchange footprint, was almost exclusively interested in Claude’s alignment layer — how it handles policy-sensitive queries, how it refuses, how it behaves at the edges. Each lab was essentially reverse-engineering not just a model but a business plan.
The MIT research documented in December 2025 found that GLM-series models identify themselves as Claude approximately half the time when queried through certain paths — behavioral residue of distillation that no fine-tuning has fully scrubbed. US officials estimate the financial toll of this campaign in the billions annually. The Trump administration’s AI Action Plan has already called for a formal inter-industry sharing center, essentially institutionalizing what the labs are now doing informally.
The geopolitical stakes here extend far beyond corporate IP. When DeepSeek released its R1 model in January 2025 — a model widely believed to incorporate distilled knowledge from OpenAI’s infrastructure — it erased nearly $1 trillion from US and European tech stocks in a single trading session. Markets now understand something that policymakers are only beginning to grasp: control over frontier AI model capabilities is a form of strategic leverage, and distillation is a vector for transferring that leverage without a single line of export-controlled chip silicon crossing a border.
Enterprise Contracts and the New AI Treadmill
The economics of Anthropic enterprise-only AI are becoming increasingly clear as 2026 revenue data enters the public domain.
| Metric | February 2026 | April 2026 |
|---|---|---|
| Anthropic Run-Rate Revenue | $14B | $30B+ |
| Enterprise Share of Revenue | ~80% | ~80% |
| Customers Spending $1M+ Annually | 500 | 1,000+ |
| Claude Code Run-Rate Revenue | $2.5B | Growing rapidly |
| Anthropic Valuation | $380B | ~$500B+ (IPO target) |
| OpenAI Run-Rate Revenue | ~$20B | ~$24-25B |
Sources: CNBC, Anthropic Series G announcement, Sacra
Anthropic’s annualized revenue has now surpassed $30 billion — having started 2025 at roughly $1 billion — representing one of the most dramatic B2B revenue trajectories in the history of enterprise software. Sacra estimates that 80% of that revenue flows from business clients, with enterprise API consumption and reserved-capacity contracts forming the structural backbone. Eight of the Fortune 10 are now Claude customers. Four percent of all public GitHub commits are now authored by Claude Code.
What Project Glasswing does, in this context, is elegant: it creates a new category of enterprise relationship — not API access, not subscription, but strategic partnership with a frontier safety lab deploying the world’s most capable unrestricted model. The 40 organizations in the Glasswing program are not merely beta testers. They are, from a revenue architecture standpoint, being trained — habituated to Mythos-class capability before it becomes generally available, embedded in their security workflows, their CI/CD pipelines, their vulnerability management systems. By the time Mythos-class models are released at scale with appropriate safeguards, the switching cost will be prohibitive.
This is the AI treadmill: each generation of frontier capability, released exclusively to enterprise partners first, creates a loyalty layer that commoditized open-source alternatives cannot easily displace. The $100 million in Glasswing credits is not charity. It is customer acquisition at an unprecedented model tier.
The Counter-View: Responsible Deployment Has a Principled Case
It would be intellectually dishonest to leave the distillation-flywheel critique standing without challenge. The counter-argument is real, and it deserves full articulation.
Platformer’s analysis makes the most compelling version of the responsible-rollout defense: Anthropic’s founding premise was that a safety-focused lab should be the first to encounter the most dangerous capabilities, so it could lead mitigation rather than react to catastrophe. With Mythos, that appears to be exactly what is happening. The company did not race to monetize these cybersecurity capabilities. It briefed government agencies, convened a defensive consortium, committed $4 million to open-source security projects, and staged rollout behind a coordinated patching effort. The vulnerabilities Mythos found in Firefox, Linux, and OpenBSD are being disclosed and patched before the paper trail of their discovery becomes public — precisely the protocol that responsible security research demands.
Alex Stamos, whose expertise in adversarial security spans decades, offered the optimistic framing: if Mythos represents being “one step past human capabilities,” there is a finite pool of ancient flaws that can now be systematically found and fixed, potentially producing software infrastructure more fundamentally secure than anything achievable through traditional auditing. That is not corporate spin. It is a coherent theory of defensive AI benefit.
The Mythos AI release strategy also reflects a genuinely novel regulatory challenge: the EU AI Act’s next enforcement phase takes effect August 2, 2026, introducing incident-reporting obligations and penalties of up to 3% of global revenue for high-risk AI systems. A general release of Mythos into that environment — without governance infrastructure in place — would be commercially catastrophic as well as potentially harmful. Enterprise-gated release buys time for both the regulatory and technical scaffolding to mature.
What Regulators and Open-Source Advocates Must Do Next
The policy implications of Anthropic Mythos extend far beyond one company’s release strategy. They illuminate a structural shift in how frontier AI capability is being distributed — and by whom, and to whom.
For regulators, the Glasswing model raises questions that existing frameworks cannot answer. If a private company now possesses working zero-day exploits for virtually every major software system on earth — as Kelsey Piper pointedly observed — what obligations of disclosure and oversight apply? The fact that Anthropic is briefing CISA and the Center for AI Standards and Innovation is encouraging, but voluntary briefings are not governance. The EU’s AI Act and the US AI Action Plan both need explicit provisions covering what happens when a commercially controlled lab becomes the de facto custodian of the world’s most significant vulnerability database.
For open-source advocates, the distillation dynamic poses an existential dilemma. The same economic logic that drives labs to gate Mythos also drives them to resist open-weights releases of any model that approaches frontier capability. The three-lab alliance against Chinese distillation is, viewed from a certain angle, also an alliance against open-source proliferation of frontier capability — regardless of the nationality of the developer doing the distilling. Open-source foundations, university research labs, and sovereign AI initiatives in Europe, the Middle East, and South Asia should be pressing hard for access frameworks that allow defensive cybersecurity use of frontier capability without being filtered through the commercial relationships of Silicon Valley.
For enterprise decision-makers, the message is unambiguous: the organizations that embed Mythos-class capability into their vulnerability management workflows now will hold a structural security advantage — measured in patch latency and zero-day coverage — over those that wait for open-source equivalents. But that advantage comes with dependency on a single private entity whose political entanglements, from Pentagon disputes to Chinese state-actor confrontations, introduce supply-chain risks that no CISO should ignore.
Anthropic may well be protecting the internet. It is certainly protecting its empire. In 2026, those two imperatives have become so entangled that distinguishing them may be the most important work left for anyone who cares about who controls the infrastructure of the digital world.
Discover more from The Economy
Subscribe to get the latest posts sent to your email.
Analysis
Singapore-Australia LNG Pact: The Indo-Pacific’s Most Important Energy Deal of 2026
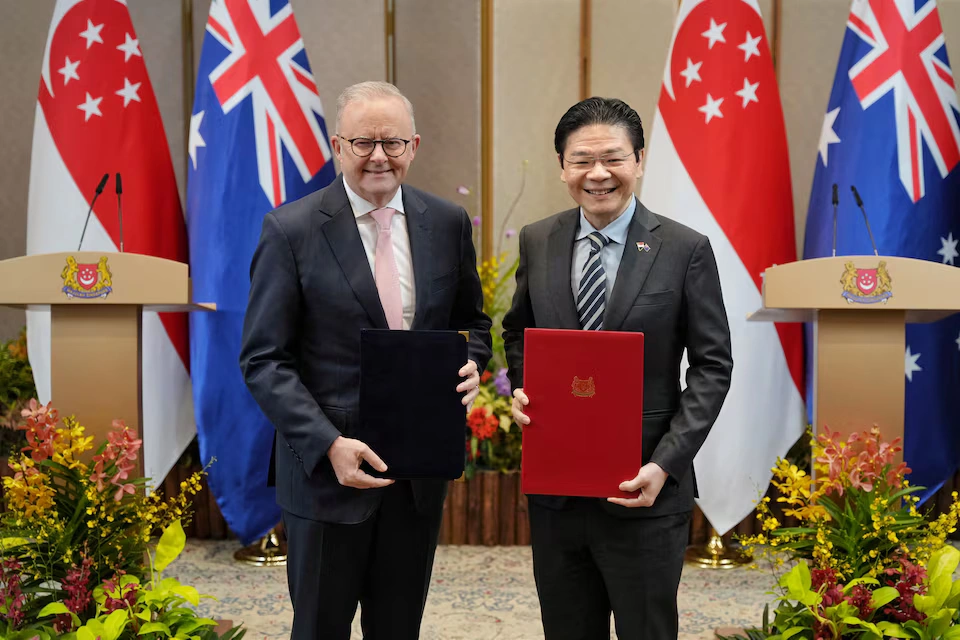
Singapore and Australia’s legally binding LNG and diesel supply agreement is rewriting Indo-Pacific energy security. Here’s why this deal matters far beyond both nations’ borders.
When Lawrence Wong stood at the Istana on Friday morning alongside Anthony Albanese and declared that this pact was “not just about managing today’s crisis, but about building trusted supply lines for a more uncertain future,” he was doing something that most politicians in 2026 conspicuously avoid: telling the complete truth. Strip away the diplomatic language, the handshakes, and the hard-hat photo opportunity at Jurong Island’s LNG terminals, and what you find underneath is something quietly historic. Two middle powers — one the world’s premier trading entrepôt, the other its third-largest LNG exporter — have decided that in an era defined by chokepoint warfare, legal commitments to energy supply are worth more than the paper they’re printed on. They may be right. And the rest of the Indo-Pacific should be paying close attention.
Why the Strait of Hormuz Has Changed Everything
To understand what Singapore and Australia agreed to on April 10, 2026, you have to first understand the world they woke up to in early March.
Until the U.S.–Israeli war against Iran, the Strait of Hormuz was open and roughly 25% of the world’s seaborne oil trade and 20% of global LNG passed through it. Wikipedia That calculus collapsed with terrifying speed. Iran’s closure of the Strait of Hormuz disrupted 20% of global oil supplies and significant LNG volumes, sending Brent crude surging past $120 per barrel and forcing QatarEnergy to declare force majeure on all exports. Wikipedia The head of the International Energy Agency called it “the greatest global energy security challenge in history.” Wikipedia
The numbers since have only grown more alarming. Dated Brent hit an 18-year high of $141.26 per barrel on April 2 MEES, while diesel prices are forecast to peak at more than $5.80 per gallon in April and average $4.80 per gallon through 2026 U.S. Energy Information Administration — devastating for the farming and mining sectors that underpin Australia’s export economy. Meanwhile, LNG spot prices in Asia more than doubled to three-year highs, reaching $25.40 per million British thermal units as QatarEnergy declared force majeure at Ras Laffan — the world’s largest liquefaction facility, responsible for 20% of global LNG production. Wikipedia

For Singapore, the crisis landed particularly hard. Singapore and Taiwan depend more on Qatari LNG than most Asian economies, Wikipedia and production at Singapore’s Jurong Island refineries has been limited because most of the oil processed there comes via the Strait of Hormuz. NEOS KOSMOS For Australia, the problem runs in the opposite but equally dangerous direction: Australia imports more than 80 percent of its petrol, diesel, and jet fuel from overseas, mostly from South Korea, Singapore, Japan, Taiwan, and Malaysia. The Diplomat A nation that sells the world its gas but can barely refine enough diesel to power its own tractors — that is the paradox at the heart of Australian energy policy, and it has never been more exposed than it is today.
The Architecture of the Singapore–Australia Legally Binding Energy Agreement
What Was Actually Agreed — and Why “Legally Binding” Matters
The joint statement issued by both prime ministers goes considerably further than the March pledge. Both leaders directed their ministers to conclude a legally binding Protocol to the Singapore-Australia Free Trade Agreement (SAFTA) on Economic Resilience and Essential Supplies, and welcomed the establishment of an Australia–Singapore Economic Resilience Dialogue, co-chaired by senior officials, to facilitate cooperation on economic resilience challenges and trade in essential supplies. Ministry of Foreign Affairs Singapore
This is not, as cynics might dismiss it, a diplomatic press release dressed in legalese. Embedding supply commitments into a protocol to an existing free trade agreement gives them treaty-level standing. In a world where spot market bidding wars are already erupting, with LNG suppliers becoming increasingly selective in negotiating mid- to long-term volumes because it’s more lucrative to sell into the spot market, Bloomberg having legal standing to demand preferential access is not a soft power gesture — it is hard economic architecture.
The underlying trade logic is elegant precisely because it is symmetrical. More than a quarter of all fuel imported into Australia comes from Singapore, while Australia provides about one-third of the city-state’s LNG supply. The Daily Advertiser Albanese articulated it plainly: “We are a big supplier of LNG to Singapore. Singapore is a really important refiner of our liquid fuels. This is a relationship of very substantial mutual economic benefit.” Both countries agreed to “make maximum efforts to meet each other’s energy security needs.” Yahoo!
The genius of this structure is that neither country is doing a favour. They are executing a swap — Australian gas for Singaporean refined products — and now writing that swap into binding international law before the next crisis hits.
What It Does Not (Yet) Do
Intellectual honesty requires acknowledging the limits. The joint statement contains no specific shipment volumes, no price-fixing mechanism, no explicit strategic reserve sharing agreement, and no stated timeline for when the SAFTA protocol will be concluded. “Working quickly” is a political phrase, not a procurement schedule.
The more fundamental challenge is Singapore’s refinery throughput. An LNG tanker can cost $250 million, and insurance concerns alone mean operations cannot simply be ramped up and down based on perceived escalations or de-escalations. CNBC Singapore is committed — but commitment is not the same as capacity. If the Strait of Hormuz remains closed into the northern hemisphere summer, Singapore’s refineries will be processing less crude regardless of which bilateral agreements are in place.
The Indo-Pacific Energy Security Realignment — China’s Shadow and AUKUS Synergy
A Geopolitical Sorting Process Is Underway
On March 4, the IRGC announced that the strait is closed to any vessel going “to and from” the ports of the U.S., Israel, and their allies. Subsequently, reports emerged that Iran would allow only Chinese vessels to pass through the strait, citing China’s supportive stance towards Iran. Wikipedia Read that sentence twice, slowly. This is not an energy story. This is a geopolitical sorting machine, restructuring the global energy map along lines of political alignment.
Australia and Singapore are unmistakably on one side of that divide. Both are Quad-adjacent, both are democracies with deep security ties to Washington, and both are now accelerating energy arrangements with each other precisely because they cannot rely on the Gulf supply corridor that Beijing is quietly privileged to use. The Singapore–Australia critical supplies pact 2026 is, in this light, a de facto statement about which bloc each country is wagering its energy future on.
This is the AUKUS undertow that neither government will name explicitly in polite company. The defence partnership’s security architecture and the energy partnership announced Friday are two different expressions of the same strategic logic: when the chips are down, trust the relationship, not the market.
Europe’s Cautionary Tale — and Australia’s Strategic Leverage
Europe is expected to suffer a second energy crisis primarily as a result of the suspension of Qatari LNG and the closure of the Strait of Hormuz. The conflict coincided with historically low European gas storage levels — estimated at just 30% capacity following a harsh 2025–2026 winter — causing Dutch TTF gas benchmarks to nearly double to over €60 per megawatt-hour by mid-March. Wikipedia
Europe’s tragedy — and it is genuinely tragic — is that it spent two years after Russia’s Ukraine invasion congratulating itself on diversification while not actually completing it. Gas storage went into the 2025–2026 winter at dangerous levels. Long-term LNG contract structures were renegotiated upward at the worst possible moment. The continent is now bidding against Asia for every available cargo on the spot market at prices that are genuinely destabilising.
Australia’s decision to negotiate supply agreements bilaterally — not just with Singapore but reportedly with Brunei, China, Indonesia, Japan, Malaysia, and South Korea — reflects a hard-won lesson from Europe’s misadventure: energy resilience is relational, not just infrastructural. Pipes and terminals matter, but so does the phone call at 3 a.m. when a chokepoint closes. Australia has spent four years building those relationships; it is now cashing them in.
As Australian Assistant Foreign Affairs Minister Matt Thistlethwaite put it: “We’ve got that advantage in that we can work with our neighbours in the Asia-Pacific to ensure that they have access to their energy needs and we get access to ours.” The Diplomat That is, in essence, the diplomatic theory of the LNG diesel supply chain security Singapore-Australia agreement: Canberra’s natural gas wealth is being converted into political insurance, denominated in refined fuel.
Why This Model Could Become the Template for Indo-Pacific Energy Diplomacy
Beyond the Free Trade Agreement — A New Class of Instrument
The standard toolkit of bilateral trade diplomacy — tariff schedules, most-favoured-nation status, investor protection clauses — was designed for a world where supply disruptions were rare, short, and solvable by price signals. The 2026 Hormuz crisis has exposed that assumption as dangerously complacent.
What the Singapore–Australia agreement proposes is something genuinely novel: a crisis-contingent preferential supply protocol, embedded within an FTA architecture but explicitly activated under conditions of global disruption. The Australia–Singapore Economic Resilience Dialogue, co-chaired at senior official level, gives this framework an institutional nervous system — a standing mechanism for early consultation and coordinated response rather than improvised crisis management.
This is the architecture Europe wishes it had built with its LNG suppliers after 2022. It is the architecture Japan and South Korea are now, belatedly, also pursuing. South Korea holds about 3.5 million tons of LNG and Japan around 4.4 million tons in reserves — enough for roughly two to four weeks of stable demand, CNBC a buffer that a single disrupted cargo schedule can obliterate. Bilateral resilience protocols of the Singapore–Australia variety provide the diplomatic scaffolding around which physical stockpile strategies must now be built.
Trusted Supply Lines: The New Competitive Advantage
Wong’s phrase — “trusted supply lines” — is going to echo through energy ministries across the Indo-Pacific for years. The word choice is deliberate. Trusted is not cheap or close or abundant. It is a relational category, not a logistical one. And in a global energy market being restructured by geopolitical conflict, relational trust is becoming the scarce commodity.
Wong was explicit: “We do not plan to restrict exports. We didn’t have to do so even in the darkest days of COVID and we will not do so during this energy crisis. I am confident that Australia and Singapore will not just get through the crisis, but we will emerge stronger and more resilient.” The Daily Advertiser That is a political commitment of the first order — a small city-state with no hinterland, surrounded by a global disruption, choosing not to hoard. It is worth more than any contract clause.
Data Snapshot: The Interdependence That Makes This Pact Work
| Flow | Volume | Significance |
|---|---|---|
| Australia → Singapore (LNG) | ~39.4% of Singapore’s LNG supply (2024) | Singapore’s largest single LNG source |
| Singapore → Australia (refined fuels) | >26% of Australia’s total fuel imports | Australia’s largest refined fuel supplier |
| Singapore → Australia (petrol) | >50% of Australia’s petrol intake | Critical for road and agricultural sectors |
| Global LNG through Hormuz | ~20% of global LNG trade | Now disrupted; Qatar’s Ras Laffan offline |
| Brent crude peak (April 2026) | $141.26/barrel (April 2 high) | 18-year high; compressing refinery margins |
The numbers tell a story of mutual exposure that makes this deal not merely politically desirable but economically unavoidable. Both economies would suffer severely without each other’s supply; the pact simply converts that mutual dependence into a formal and enforceable commitment.
Forward Look: Three Bold Predictions
First: The Singapore–Australia protocol will be concluded within 90 days and will serve as the explicit template for at least two additional bilateral energy resilience agreements in the Indo-Pacific — most likely involving Japan and either South Korea or New Zealand — by the end of 2026. The institutional architecture of the Economic Resilience Dialogue is designed to be replicated.
Second: The Hormuz crisis will accelerate Australia’s long-stalled domestic refining debate. Having 80% of your liquid fuel supply dependent on overseas refiners — however trusted — is a structural vulnerability that no bilateral agreement can fully paper over. Expect a serious federal government investment framework for domestic refining capacity to emerge within 18 months, framed explicitly as national security infrastructure.
Third: China is watching this closely and will not be idle. Beijing already enjoys de facto preferential passage through the Strait for its tankers. If it perceives that a Singapore–Australia–Japan energy axis is forming along security-aligned lines, it will accelerate its own bilateral energy lock-in arrangements with alternative suppliers — deepening the global energy bifurcation that began in 2022 and is now accelerating at pace. The Indo-Pacific energy security agreement between Wong and Albanese is not just a supply pact. It is an early data point in the restructuring of the global energy order.
Conclusion: A Small Pact With a Very Large Shadow
There is something almost anachronistic about two democracies in 2026 sitting down together and saying, plainly, that they will keep trade flowing — that they will not weaponise energy in the way that others have. It is the kind of statement that would have seemed unremarkable in 2015. Today it feels almost radical.
The Singapore–Australia LNG and diesel agreement signed at the Istana is, in its immediate terms, a sensible and well-constructed piece of crisis diplomacy. In its deeper terms, it is a proof of concept: that trusted bilateral relationships, properly institutionalised, can serve as genuine shock absorbers in a world where the multilateral system is fraying and chokepoints are being used as weapons.
PM Wong called it a “simple but critical principle.” He is right on both counts. Simple principles, rigidly held under pressure, are often the most valuable ones. And right now, in a global energy market that has been turned upside down in six weeks, the principle that allies keep their promises to each other may be the most critical thing the Indo-Pacific has.
The rest of the world’s energy ministers should take note — and consider what it would mean to have nobody to call when their own Hormuz moment arrives.
Discover more from The Economy
Subscribe to get the latest posts sent to your email.
AI
Anthropic Rolls Out Its Most Powerful Cyber AI Model — Days After Leaking Its Own Source Code
The launch of Claude Mythos Preview and Project Glasswing, mere days after Anthropic accidentally exposed 512,000 lines of its core product’s source code to the world, is either the most audacious act of strategic redirection in Silicon Valley history — or the most revealing window yet into the contradictions at the heart of frontier AI development.
There is a particular species of Silicon Valley irony that only manifests at the very frontier of technological ambition. On March 31st, 2026, an Anthropic employee made a mistake so elementary it would embarrass a first-year computer science undergraduate: a debug source map file was accidentally bundled into a public software release, pointing to a cloud-hosted archive of the company’s most commercially prized product — the source code of Claude Code, its flagship agentic coding assistant. Within hours, 512,000 lines of proprietary TypeScript code, across 1,906 files, were mirrored, forked, and torrent-distributed across the internet, never to be recalled. The repository on GitHub was forked more than 41,500 times before Anthropic could blink. Then, seven days later, Anthropic announced the most capable AI model it has ever built — a cybersecurity behemoth called Claude Mythos Preview — and launched Project Glasswing, a sweeping initiative to secure the world’s critical digital infrastructure. The company publicly described it as a watershed for global security. A watching world could be forgiven for raising an eyebrow.
History rarely serves up irony quite this rich. The firm that accidentally handed a blueprint of its proprietary agent harness to thousands of developers, threat actors, and competitors — the firm that inadvertently revealed the internal codename of its most powerful unreleased model buried in that same code — emerged days later as the standard-bearer for a new era of AI-powered cyber defence. It is, depending on your interpretation, either a masterclass in narrative control or a deeply unsettling indicator of the structural tensions now embedded in the development of frontier AI.
I. A Double Embarrassment: The Anatomy of the Leak
The facts of the Anthropic source code leak are simultaneously mundane and extraordinary. On the morning of March 31st, 2026, Anthropic pushed version 2.1.88 of its @anthropic-ai/claude-code package to the npm public registry. Buried inside was a 59.8-megabyte JavaScript source map file — a developer debugging tool that, when followed to its reference URL on Anthropic’s own Cloudflare R2 storage bucket, yielded a downloadable zip archive of the complete, unobfuscated TypeScript source for Claude Code.
Security researcher Chaofan Shou, an intern at Solayer Labs, spotted the exposure at 4:23 AM Eastern and posted a direct download link on X. It was, as The Register reported, “a mistake as bad as leaving a map file in a publish configuration” — a single misconfigured .npmignore field. A known bug in Bun, the JavaScript runtime Anthropic had acquired in late 2025, had been causing source maps to ship in production builds for twenty days before the incident. Nobody caught it.
This was, in fact, the second major accidental disclosure of the month. Days earlier, Fortune had reported on a separate leak of nearly 3,000 files from a misconfigured content management system — including a draft blog post describing a forthcoming model described internally as “by far the most powerful AI model” Anthropic had ever developed. That model’s codename: Mythos. Also, apparently: Capybara.
The March–April 2026 Anthropic Disclosure Timeline
| Date | Event |
|---|---|
| ~Late March 2026 | Fortune reports on ~3,000 leaked CMS files; first public confirmation of the Mythos model’s existence and capabilities. |
| March 31, 2026 | Claude Code v2.1.88 ships to npm with embedded source map; 512,000 lines of TypeScript exposed within hours. GitHub repository forked 41,500+ times. |
| March 31 – April 6 | Anthropic issues DMCA takedowns; threat actors seed trojanized forks with backdoors and cryptominers. Axios supply-chain attack occurs simultaneously. |
| April 7, 2026 | Anthropic officially announces Claude Mythos Preview and Project Glasswing. Partners include Apple, Microsoft, Google, Amazon, JPMorgan Chase, and others. |
What the leaked source revealed was considerable: 44 hidden feature flags for unshipped capabilities, a sophisticated three-layer memory architecture, the internal orchestration logic for autonomous “daemon mode” background agents, and — critically — confirmation that a model called Capybara was actively being readied for launch. The VentureBeat analysis noted that Claude Code had achieved an annualised recurring revenue run rate of $2.5 billion by March 2026, making the intellectual property exposure a genuinely material event for a company preparing to go public.
II. Claude Mythos Preview and Project Glasswing: A Technical Step-Change
To understand why the timing of the Mythos announcement matters, one must first grasp the scale of what Anthropic is claiming. Claude Mythos Preview is not a marginal improvement on its predecessors. It occupies, in Anthropic’s internal taxonomy, a fourth tier entirely above the existing Haiku–Sonnet–Opus range — a tier the company internally designates “Copybara.” According to SecurityWeek, it represents “not an incremental improvement but a step change in performance.”
The headline claim is breathtaking in its scope. In the weeks prior to the public announcement, Anthropic ran Mythos against real open-source codebases and, according to its own Project Glasswing announcement, the model identified thousands of zero-day vulnerabilities — flaws previously unknown to software maintainers — across every major operating system and every major web browser. The oldest vulnerability it uncovered was a 27-year-old bug in OpenBSD, a system famous for its security record. A 16-year-old flaw in video processing software survived five million automated test attempts before Mythos found it in a matter of hours. The model autonomously chained together a series of Linux kernel vulnerabilities into a privilege escalation exploit — the kind of attack chain that would previously have required a sophisticated, nation-state-grade human research team.
A single AI agent could scan for vulnerabilities and potentially take advantage of them faster and more persistently than hundreds of human hackers — and similar capabilities will be available across the industry in as little as six months.
The Axios reporting on the rollout puts the dual-use risk with uncomfortable clarity: Mythos is “extremely autonomous” and possesses the reasoning capabilities of an advanced security researcher, capable of finding “tens of thousands of vulnerabilities” that even elite human bug hunters would miss. This is precisely why Anthropic chose not to release it publicly. Instead, Project Glasswing gives curated preview access to 40-plus organisations responsible for critical software infrastructure — including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorgan Chase, the Linux Foundation, Microsoft, Nvidia, and Palo Alto Networks — backed by up to $100 million in usage credits and $4 million in direct donations to open-source security organisations including the Apache Software Foundation and OpenSSF.
The model is not cybersecurity-specific. CNBC noted that Mythos’s cyber prowess is a downstream consequence of its exceptional general-purpose coding and reasoning capabilities — a distinction with profound regulatory implications. You cannot restrict a model trained to think brilliantly about code from thinking brilliantly about vulnerabilities in that code.
III. The Deeper Meaning: Irony, Competence, and the New Security Paradigm
The central paradox demands direct engagement: Anthropic, a company whose founding proposition is responsible AI development, leaked its own product’s source code through a packaging error so elementary it required no sophistication to exploit. It then, within the same news cycle, announced an AI model so powerful its own CEO fears its public release — and positioned itself as the primary steward of global cyber defence. One is entitled to hold both thoughts simultaneously.
And yet the strategic coherence of the Mythos launch, viewed against the backdrop of the leak, is hard to dismiss entirely. Anthropic did not choose the timing. The Mythos project had been in development and partner testing for weeks before the Claude Code source code escaped its containment. But the company, having already suffered the reputational bruise of one accidental exposure too many, had an imperative to seize the narrative — to move from embarrassed leaker to principled guardian, rapidly. The result is a masterclass in what crisis communications professionals call “agenda replacement.”
The deeper issue, however, is structural and it transcends any single company. The Axios assessment is stark: Mythos is “the first AI model that officials believe is capable of bringing down a Fortune 100 company, crippling swaths of the internet or penetrating vital national defense systems.” Meanwhile, the head of Anthropic’s frontier red team, Logan Graham, told multiple outlets that comparable capabilities will be in the hands of the broader AI industry within six to eighteen months — from every nation with frontier ambitions, not just the United States. The window for getting ahead of this threat is not a decade. It is, at most, a year.
What the Mythos launch crystallises is a principle that the cybersecurity community has long understood but that corporate AI leaders and policymakers have been reluctant to internalise: the same model property that makes an AI system valuable for defence makes it catastrophically useful for offence. The technical writeup on Anthropic’s red team blog makes this explicit. Mythos can “reverse-engineer exploits on closed-source software” and turn known-but-unpatched vulnerabilities into working exploits. Gadi Evron, founder of AI security firm Knostic, told CNN that “attack capabilities are available to attackers and defenders both, and defenders must use them if they’re to keep up.” There is no asymmetry available — only the question of who moves first.
IV. The Geopolitical and Regulatory Reckoning
The implications of Anthropic Mythos extend well beyond corporate strategy. The U.S.-China AI competition has already entered the domain of active cyber operations. A Chinese state-sponsored group, as Fortune reported, used an earlier Claude model to target approximately 30 organisations in a coordinated espionage campaign before Anthropic detected and curtailed the activity. If a Claude model that predates Mythos by several capability generations was sufficient to mount a significant intelligence operation, the implications of Mythos-class capability in hostile hands are genuinely alarming.
A source briefed on Mythos told Axios: “An enemy could reach out and touch us in a way they can’t or won’t with kinetic operations. For most Americans, a conventional conflict is ‘over there.’ With a cyberattack, it’s right here.” This framing matters. The doctrine of nuclear deterrence rested partly on the difficulty of acquisition. The doctrine of cyber deterrence in the Mythos era rests on nothing — the marginal cost of deploying AI-accelerated attack capability approaches zero for any state or non-state actor with API access to a comparable model.
Anthropic’s relationship with Washington is, to put it diplomatically, complicated. The company is simultaneously briefing the Cybersecurity and Infrastructure Security Agency, the Commerce Department, and senior officials across the federal government on Mythos’s capabilities — while locked in active litigation with the Pentagon, which has labelled Anthropic a supply-chain risk following the company’s refusal to permit autonomous targeting or battlefield surveillance applications. The AI safety firm that declined to arm American drones is now, in the same breath, offering American critical infrastructure a first-mover advantage against AI-powered adversaries. The philosophical coherence of this position is defensible; its political navigation will be considerably harder.
For regulators, the Mythos announcement poses a question for which existing frameworks have no satisfying answer. The EU AI Act’s tiered risk classifications were not designed for a model that is simultaneously a breakthrough productivity tool, a national security asset, and a potential weapon of mass cyber-disruption. The Project Glasswing model — voluntary, industry-led, access-gated — is a plausible short-term mechanism. It is not a durable regulatory framework. And as Logan Graham made clear, the window before other frontier labs — and the Chinese state — reach comparable capability is measured in months, not years.
V. Verdict: A Reckoning Dressed as a Launch
Editorial Assessment
The Mythos announcement is not primarily a product launch. It is a reckoning — one that Anthropic has had the narrative dexterity to package as a strategic initiative rather than a confession. The source code leak was, at the level of operational security, an embarrassment of the first order. But it was also, unintentionally, a proof of concept for the vulnerability landscape that Mythos was built to address. Anthropic’s own systems failed a test far simpler than any that Mythos could conceivably pose to a determined adversary.
That irony is not merely cosmetic. It is instructive. No organisation — not even a frontier AI lab whose entire value proposition rests on the responsible management of powerful systems — is immune to the mundane failure modes of human error, toolchain misconfiguration, and the accumulated technical debt of moving too fast. The question is not whether Anthropic can be trusted with Mythos. The question is whether any institution, in any country, is structurally capable of managing the governance of AI capabilities that are advancing faster than the legal and regulatory architectures designed to contain them.
Dario Amodei framed the Project Glasswing rollout as an opportunity to “create a fundamentally more secure internet and world than we had before the advent of AI-powered cyber capabilities.” This is not rhetorical excess. It is, technically, accurate: the same capability that can chain together a 27-year-old kernel vulnerability into a privilege escalation exploit can, in the hands of defenders, systematically eliminate such vulnerabilities from the world’s most important software. The question is not whether this technology is transformative. It is whether the institutional infrastructure required to ensure that transformation benefits defenders more than attackers can be assembled in the time available.
Six months. Eighteen at the outside. That is the horizon Logan Graham has placed on the proliferation of Mythos-class capabilities across the industry. The global financial cost of cybercrime already runs to an estimated $500 billion annually, a figure that was compiled before any model approached Mythos’s level of autonomous vulnerability discovery. Policymakers in Washington, Brussels, and Beijing who are not currently treating this as an emergency are, as one source briefed on Mythos told Axios with commendable directness, “not remotely ready.”
Anthropic rolled out its most powerful cyber AI model days after leaking its own source code. The irony is real. So is the threat. And so, potentially, is the opportunity — if the institutions responsible for governing it can move at the speed the technology demands, rather than the speed at which governments customarily prefer to operate. History suggests that gap will be considerable. The Mythos timeline suggests that gap may, for once, be decisive.
Discover more from The Economy
Subscribe to get the latest posts sent to your email.
-

 Markets & Finance3 months ago
Markets & Finance3 months agoTop 15 Stocks for Investment in 2026 in PSX: Your Complete Guide to Pakistan’s Best Investment Opportunities
-

 Analysis2 months ago
Analysis2 months agoBrazil’s Rare Earth Race: US, EU, and China Compete for Critical Minerals as Tensions Rise
-

 Banks3 months ago
Banks3 months agoBest Investments in Pakistan 2026: Top 10 Low-Price Shares and Long-Term Picks for the PSX
-

 Investment3 months ago
Investment3 months agoTop 10 Mutual Fund Managers in Pakistan for Investment in 2026: A Comprehensive Guide for Optimal Returns
-

 Analysis2 months ago
Analysis2 months agoTop 10 Stocks for Investment in PSX for Quick Returns in 2026
-

 Asia3 months ago
Asia3 months agoChina’s 50% Domestic Equipment Rule: The Semiconductor Mandate Reshaping Global Tech
-

 Global Economy3 months ago
Global Economy3 months agoPakistan’s Export Goldmine: 10 Game-Changing Markets Where Pakistani Businesses Are Winning Big in 2025
-

 Global Economy3 months ago
Global Economy3 months ago15 Most Lucrative Sectors for Investment in Pakistan: A 2025 Data-Driven Analysis












